We have discussed Managed Identity authentication for Azure Data Factory in a previous post (which was about setting up DB permissions for a linked service). Managed Identity is one of the security principals used to manage access on the Azure cloud.
Azure provides a comprehensive access control system for managing access using in-built roles. This is known as, Role Based Access Control or RBAC. RBAC is an authorization system for authentication and access control to various resources on Azure. In this post, let’s have a look at how RBAC works.
RBAC works on basis of role assignments. There are three main concepts that we should discuss to understand role assignment:
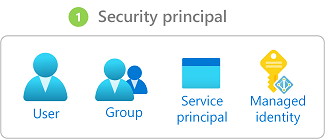
- Security Principal: This is an object which represents an entity that needs to be provided access to the Azure resource. This entity can be a user, group, service principal or a managed identity.
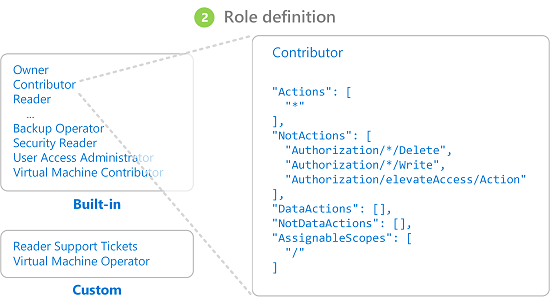
- Role Definition: A role is a collection of security permissions. The role definition specifies explicit lists of operations that can or cannot be performed by the specific role. It is somewhat like ALLOW or DENY permissions in SQL Server /SQL Azure databases. There is a whole list of built-in roles that can be used to control access to Azure Resources. E.g. Data Factory Contributor role controls who can create and manage data factories and child resources within the Data Factory.
- Scope: Scope defines, at what level the access applies to. It can be at the top level (Management Group/Subscription) or at a sub-level such as a Resource Group or a particular Resource.

Role Assignment is the process of assigning a role to a security principal (user, group, service principal or managed identity). Access is controlled through role assignments. To provide access, create a role assignment, and to revoke access, just remove the role assignment.
There are multiple ways to assign roles, through the UI (Azure portal) as well as programmatically (Azure CLI, Azure PowerShell, Azure SDKs, or REST APIs).
Reference: https://docs.microsoft.com/en-us/azure/role-based-access-control/overview